Managed IT Support Services for Optimized Business Efficiency and Security
Managed IT support services provide businesses with expert assistance in maintaining and optimizing their technology infrastructure. They handle tasks such as network monitoring, software updates, and security management to ensure systems run smoothly and securely.
These services help reduce downtime, improve efficiency, and allow companies to focus on their core operations without worrying about IT issues. By outsourcing IT support, organizations gain access to specialized knowledge and faster problem resolution.
With technology evolving rapidly, relying on managed IT support services is becoming essential for businesses that want to stay competitive and secure. This approach offers predictable costs and scalable solutions tailored to specific needs.
What Are Managed IT Support Services?
Managed IT support services provide businesses with ongoing IT management, maintenance, and troubleshooting through an external provider. These services focus on preventing issues, optimizing systems, and ensuring reliable IT operations.
Types of Managed IT Support
Managed IT support includes various service types tailored to business needs. Common offerings are:
- Network Monitoring and Management: Continuous oversight of infrastructure to detect and fix faults quickly.
- Help Desk Support: User assistance for software, hardware, or connectivity problems.
- Cybersecurity Management: Protection against threats through firewalls, antivirus, and vulnerability scanning.
- Cloud Services Management: Administration of cloud infrastructure and services like backups and migrations.
- Data Backup and Recovery: Regular backup to secure data and restore systems after failures.
Each type may be combined or chosen independently, depending on the company’s technology environment and goals.
Benefits of Managed IT Support
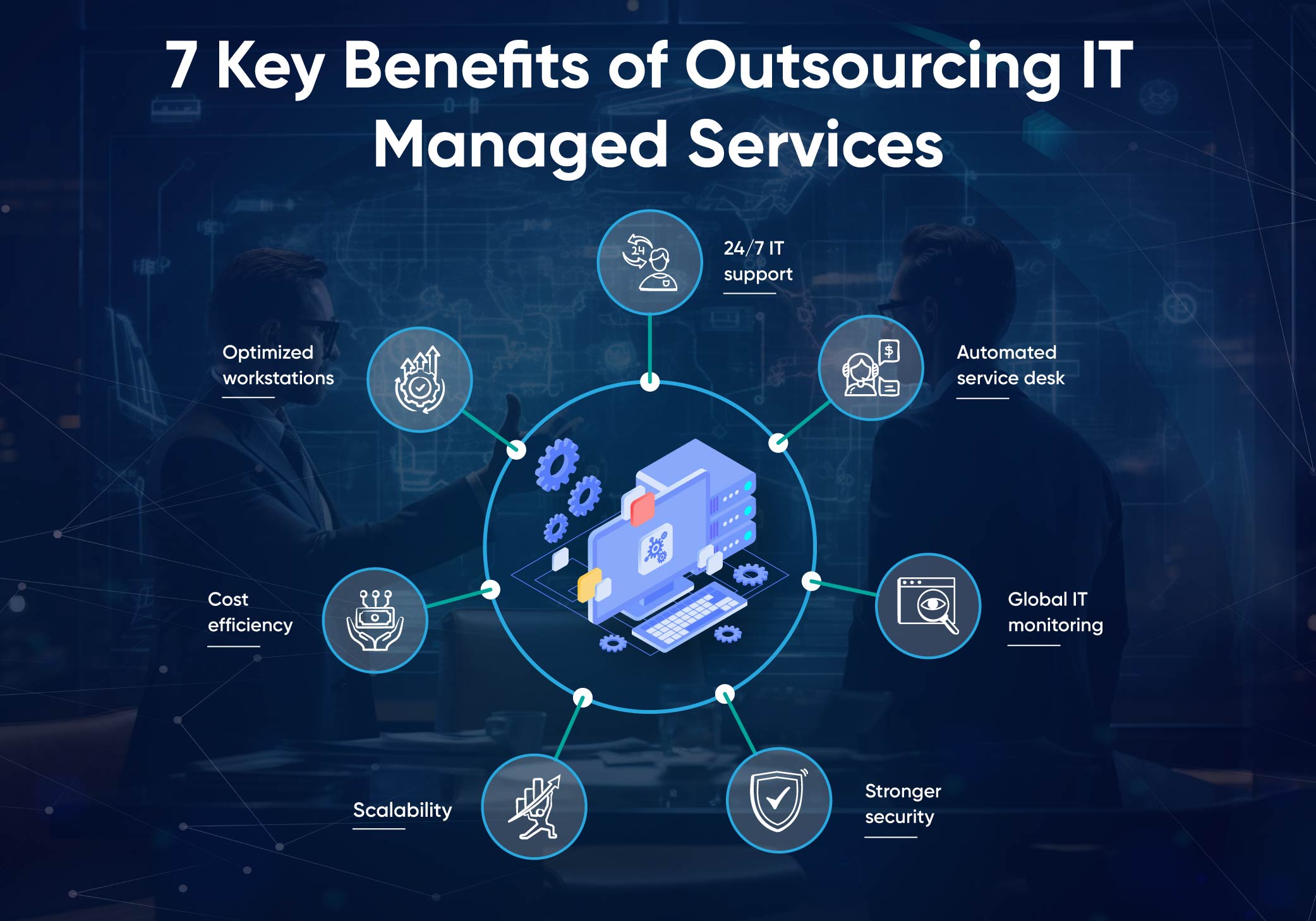
Organizations using managed IT support gain predictable costs through fixed monthly fees, streamlining budgeting. They also reduce downtime with proactive monitoring that identifies and resolves problems early.
Expertise and access to advanced technology improve security and compliance, reducing risks from cyberattacks. Additionally, outsourcing IT support allows internal staff to focus on core business functions without distraction from day-to-day IT issues.
Scalability is another advantage; services can adjust quickly to support growth or changes in technology needs.
Key Features and Capabilities
Managed IT services often include 24/7 monitoring to catch issues around the clock. Automated alerts and detailed reporting help track system health and performance metrics.
Service Level Agreements (SLAs) define response times and resolution standards, ensuring accountability. Providers typically use remote management tools to solve problems without onsite visits.
Other core capabilities involve patch management to keep software updated, asset management to track hardware and software, and disaster recovery planning to minimize data loss in emergencies.
Choosing the Right Managed IT Support Provider
Selecting a managed IT support provider requires careful attention to contract terms, security policies, and the provider’s track record. Each of these elements plays a crucial role in ensuring reliable, secure, and cost-effective IT management.
Service Level Agreements and Pricing Models
Service Level Agreements (SLAs) define the scope and quality of services a provider delivers. They must include response times, resolution times, uptime guarantees, and penalties for unmet standards. Clear SLAs protect the client by setting measurable performance standards.
Pricing models vary between flat-rate monthly fees, pay-as-you-go, or tiered pricing. Flat-rate fees offer predictable costs but may limit flexibility. Pay-as-you-go models suit businesses with variable needs but can lead to higher expenses during peak times. Clients should review terms to avoid hidden fees.
Examining both SLAs and pricing ensures transparency and aligns expectations with the provider’s capabilities.
Security and Compliance Considerations
Security measures must include real-time monitoring, incident response, and regular vulnerability assessments. Providers should demonstrate adherence to industry standards like ISO 27001, GDPR, or HIPAA where applicable.
Compliance is critical for regulated industries. The provider must show evidence of compliance audits, employee training programs, and data protection protocols. Failure to meet legal requirements causes risks including fines and reputational damage.
Businesses should verify the provider’s security certifications and ask for documented proof of compliance efforts.
Evaluating Provider Experience and Reputation
Experience is measured not only by years in business but also by relevant industry expertise and client portfolio. Providers with proven experience in similar sectors understand specific challenges and regulatory demands.
Reputation can be assessed through client testimonials, third-party reviews, and case studies. Independent platforms like Gartner Peer Insights or Trustpilot offer impartial feedback.
It is beneficial to request references and inquire about the provider’s problem-solving history, uptime record, and customer service responsiveness.
